Blog
Security
The Mythos Zero-Day Flood Is Here. Only AI Can Fix It.
Mythos and Glasswing are producing zero-days faster than any team can patch manually. The only viable defense now runs at machine speed.
6 min read

Mythos and Project Glasswing have taken the security world by storm.
We've already seen one step-change in offensive capability from AI. A few weeks ago, I wrote about the vibe hacker: the low-skill attacker who uses AI to punch above their weight class. The recent breach of the Mexican government was the clearest example. An operator with no real offensive tradecraft used Claude Code to exfiltrate 150GB of government data, and when they got stuck trying to move deeper into the compromised network, they opened a ChatGPT session and asked for help. A year earlier, that person couldn't have breached a single agency.
Anthropic’s new Mythos model takes the problem to a whole other level. Defenders are already struggling to keep up. They’re about to face a problem that's an order of magnitude worse.
Mythos: The Straw that Broke the Camel’s Back
Before Mythos, defenders were already drowning. The average enterprise takes over 60 days to remediate a critical vulnerability and 60% of breaches involve exploiting known vulnerabilities where a patch was already available. Large enterprises maintain backlogs where 45% of identified vulnerabilities remain unpatched after twelve months. Two forces have been converging to widen the gap between what defenders can fix and what attackers can exploit.
The volume of new CVEs published annually is surging, driven largely by AI. Last year, XBOW became the top researcher on HackerOne's US leaderboard, the first autonomous system to outperform every human hacker on the platform. Meanwhile, time to exploit has collapsed from 2.4 years in 2018 to under a day in 2026. AI can reverse-engineer a patch to identify the underlying vulnerability within hours of release.
Anthropic's Claude Mythos Preview found zero-day vulnerabilities in every major operating system and every major web browser, autonomously. According to Anthropic's red team, Mythos chained four separate vulnerabilities into a working browser exploit that broke through multiple layers of security isolation with no human involvement.
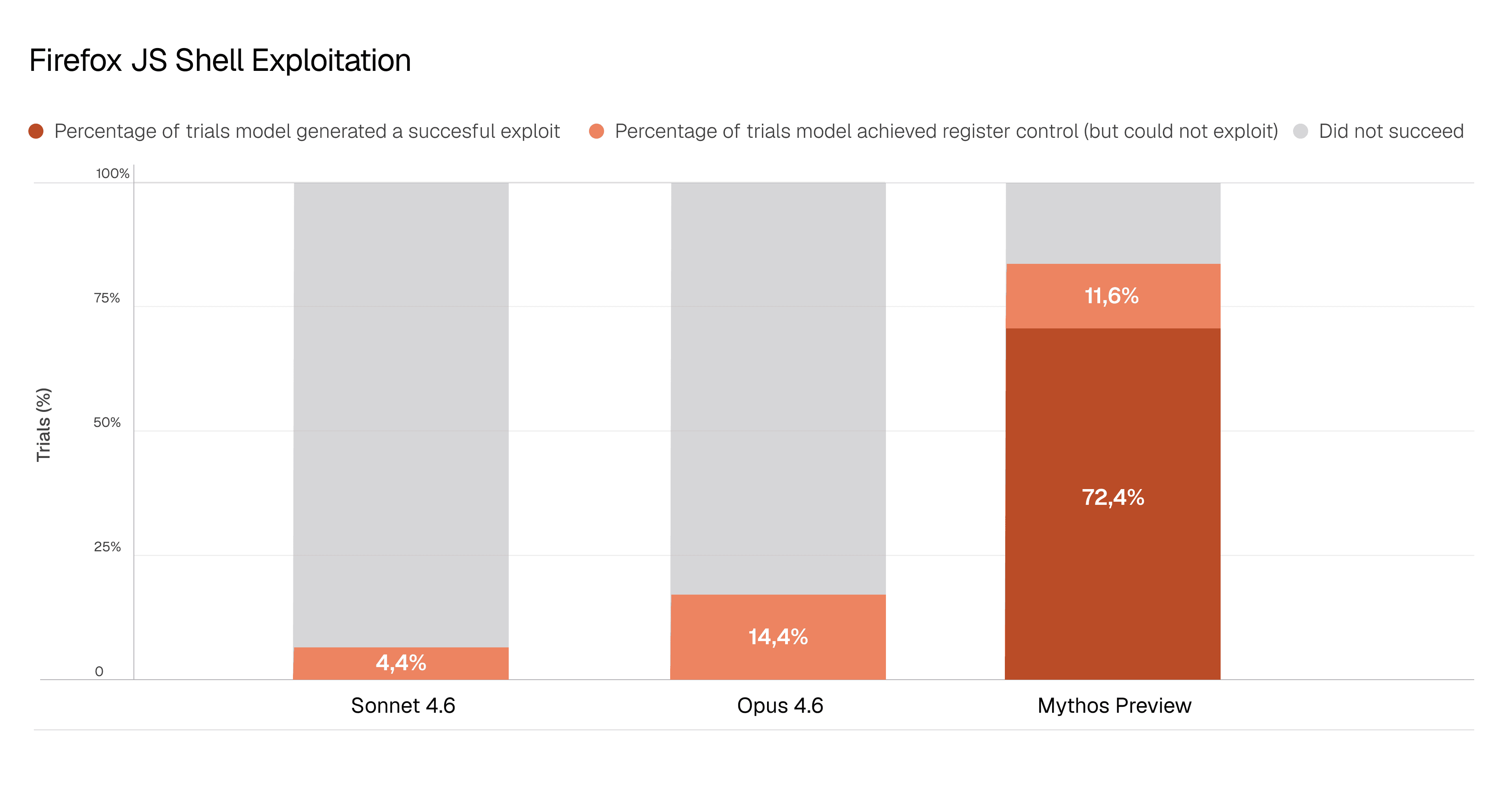
The capability jump from previous models is stark. Anthropic's Opus 4.6 had a near-zero success rate at autonomous exploit development. On the same Firefox benchmark, Opus succeeded twice out of several hundred attempts. Mythos successfully generated an exploit 181 times. A 27-year-old bug in OpenBSD, an operating system built around security, had gone undetected by every human researcher and automated tool for nearly three decades. Mythos found it.
How AI Reshapes the Attacker Hierarchy
Before Mythos, discovering unknown vulnerabilities and autonomously building working exploits that chain multiple bugs together has historically required dedicated research teams funded by intelligence agency budgets. It was the province of nation-state programs with years of institutional knowledge and millions in resources.
Currently available AI models have already raised the floor of what attackers are capable of. "Script kiddies" who once relied on off-the-shelf exploit code for published vulnerabilities now have the ability to automate reconnaissance, generate custom tooling, and execute attacks that would have been out of reach twelve months ago. This is the “vibe-hacking” era.
Mythos previews a world where AI will raise the ceiling of what even sophisticated attackers can do. Organized cybercrime groups that previously topped out at exploiting known vulnerabilities can now access autonomous zero-day discovery and exploit chaining, a capability that has defined nation-state programs. Nation-state operations involve more than exploit sophistication: intelligence-driven targeting, operational security, infrastructure across dozens of countries. But exploit development was a significant barrier separating these tiers, and that barrier is eroding.
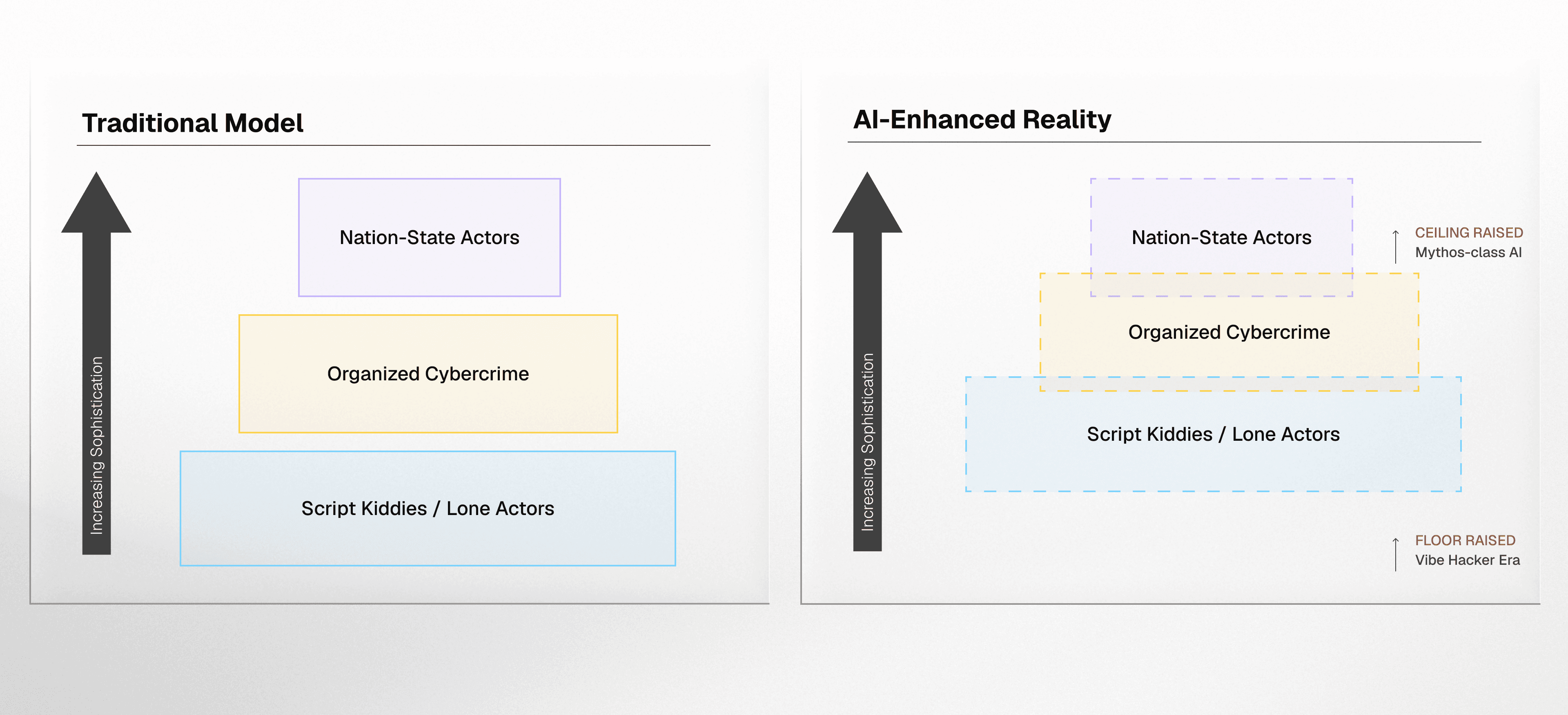
Today, Mythos-class capabilities are restricted. Anthropic has limited access to vetted partners through Project Glasswing. But frontier model capabilities have a consistent pattern of proliferating. What a leading lab can do today, freely available open-source models tend to match within twelve to eighteen months. When that happens, autonomous zero-day discovery and exploit chaining will be available to anyone with a GPU.
Why Only AI-driven Remediation Can Solve the Gap
The traditional response to an accelerating threat environment has been to invest in detection and response. That has meant better SOC tooling, faster incident response, more sophisticated threat hunting. If you can't stop every breach, at least minimize the blast radius. That logic made sense when exploitation windows were measured in weeks. It doesn't hold when they're measured in hours.
When mean time to exploit collapses to under a day, incident response becomes damage control. Your SOC detects anomalous behavior, pivots to investigation, confirms the breach, and begins containment. By then, the attacker has already moved. Detection and response assumes there is time between intrusion and impact. Mythos-class AI is eliminating that window.
Most vulnerability management programs are already underwater. Security teams sit on backlogs of thousands, sometimes hundreds of thousands, of known vulnerabilities they haven’t been able to remediate. The engineering teams who actually apply fixes are stretched thin, competing with feature work and operational demands. Remediation capacity has been the bottleneck for years, and Mythos-class AI is about to make it significantly worse.
The closest historical precedent is Y2K. Organizations mobilized to patch a single systemic flaw embedded across every system before a fixed deadline. What's coming is Y2K without the fixed deadline, without the single flaw, without the bounded scope. It's a continuous flood of critical vulnerabilities arriving faster than any patch cycle was built to handle, each one with an exploit window measured in hours.
Remediation is the only strategy that closes the gap before it opens. Fixing a vulnerability before it's exploited costs a fraction of what a breach costs. The economics have always favored remediation. The problem has been that remediation at scale was never operationally possible.
Cogent: Automating Remediation
The math is straightforward. Enterprises remediate roughly 16% of their vulnerability backlog per month. Critical vulnerabilities take months to fix. Meanwhile, exploitation now begins within hours of disclosure. No amount of additional headcount closes that gap when inbound volume is increasing by an order of magnitude and the remediation window is collapsing simultaneously. Human-speed remediation workflows cannot absorb machine-speed vulnerability discovery. The only way to match the tempo of AI-driven offense is with AI-driven defense.
Cogent was built at the intersection of these two disciplines. Our founding team includes researchers from Google DeepMind who left one of the most prestigious AI labs in the world to work on this problem, alongside engineers who built ML systems used by half the Fortune 500. The reason they came to Cogent is structural: the best AI talent clusters in big tech labs, but those labs don't have access to real enterprise security operations data. Security vendors have the domain expertise and the data, but not the frontier AI research capability.
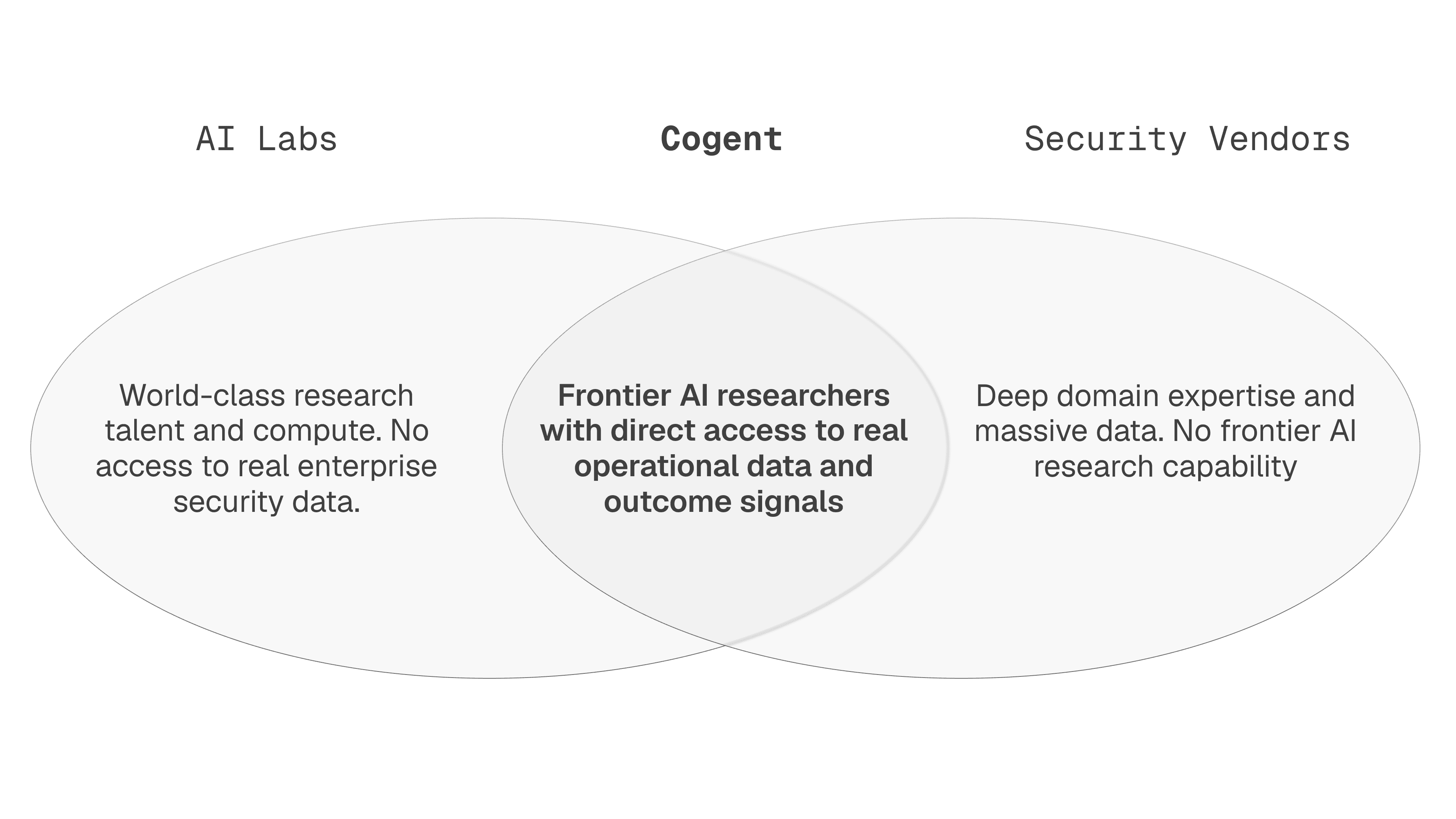
Cogent combines both. The defensive response to Mythos-class threats requires a platform that can identify zero-days in your environment before your scanner even knows they exist. That means not waiting for scanner vendors to write new detection signatures. Instead, it means inferring exposure directly from the software packages running in your environment, scoring findings against your actual infrastructure rather than a generic CVSS number, and driving remediation autonomously from discovery all the way to verified closure.
Surviving the coming surge won’t come down to how many analysts are reviewing dashboards. It will come down to how quickly your systems can detect a newly disclosed vulnerability, determine where it exists in your environment, and initiate a fix before the exploit is circulating.
That's the direction we're building toward at Cogent. We'll have more to share soon.
What Comes Next
Mythos is one model from one lab, and Anthropic has handled the release responsibly by giving defenders early access. Comparable capabilities will emerge in other frontier models within months. Open-source models will follow. The offensive capability curve is not slowing down.
The floor was raised last year. The ceiling is being raised now. The organizations that come through this well won't be the ones that hired more analysts or ran more scans. They'll be the ones that recognized the remediation bottleneck as the real constraint and deployed AI to break through it before the wave hit.







